C99 Shell is not Dead
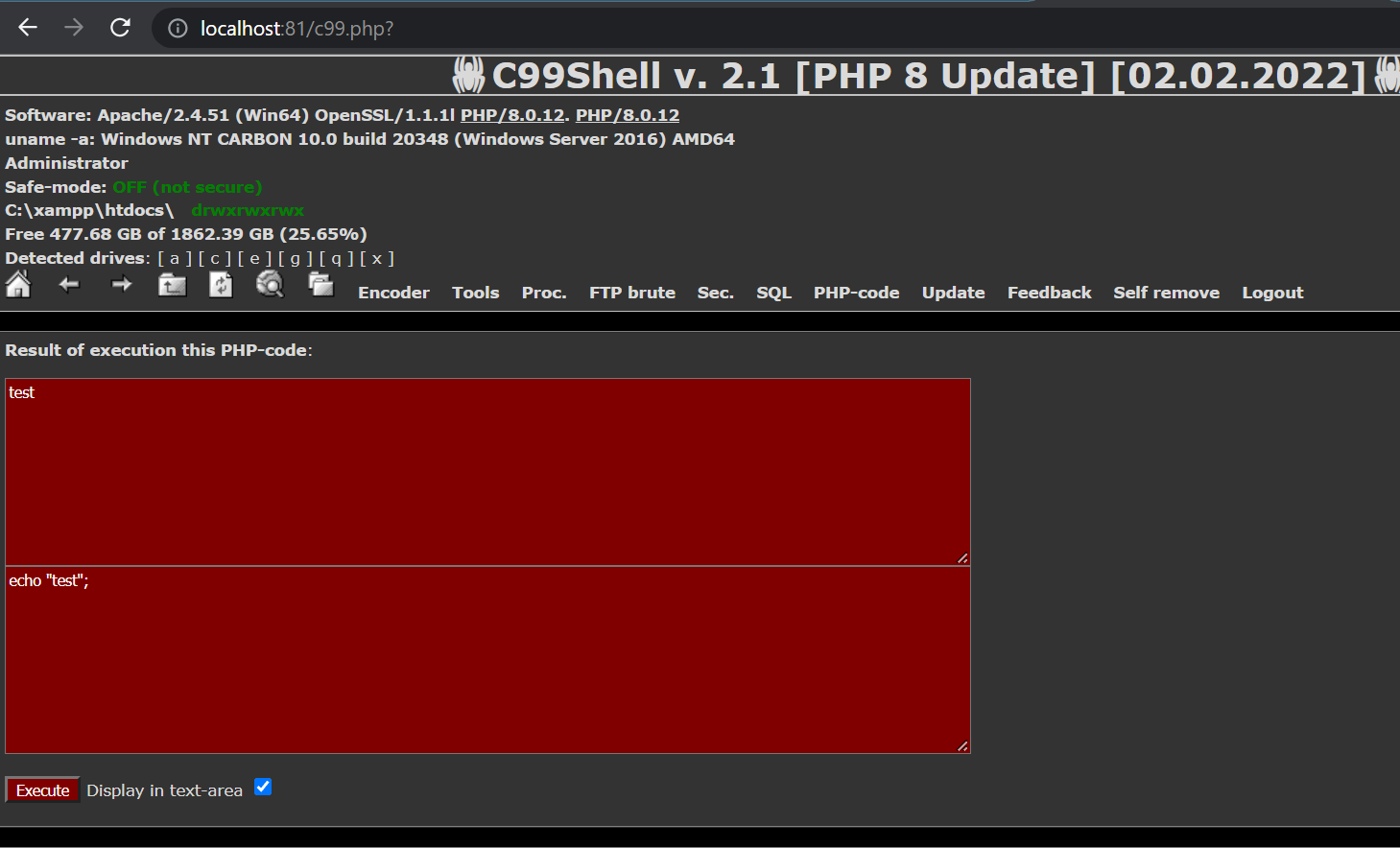
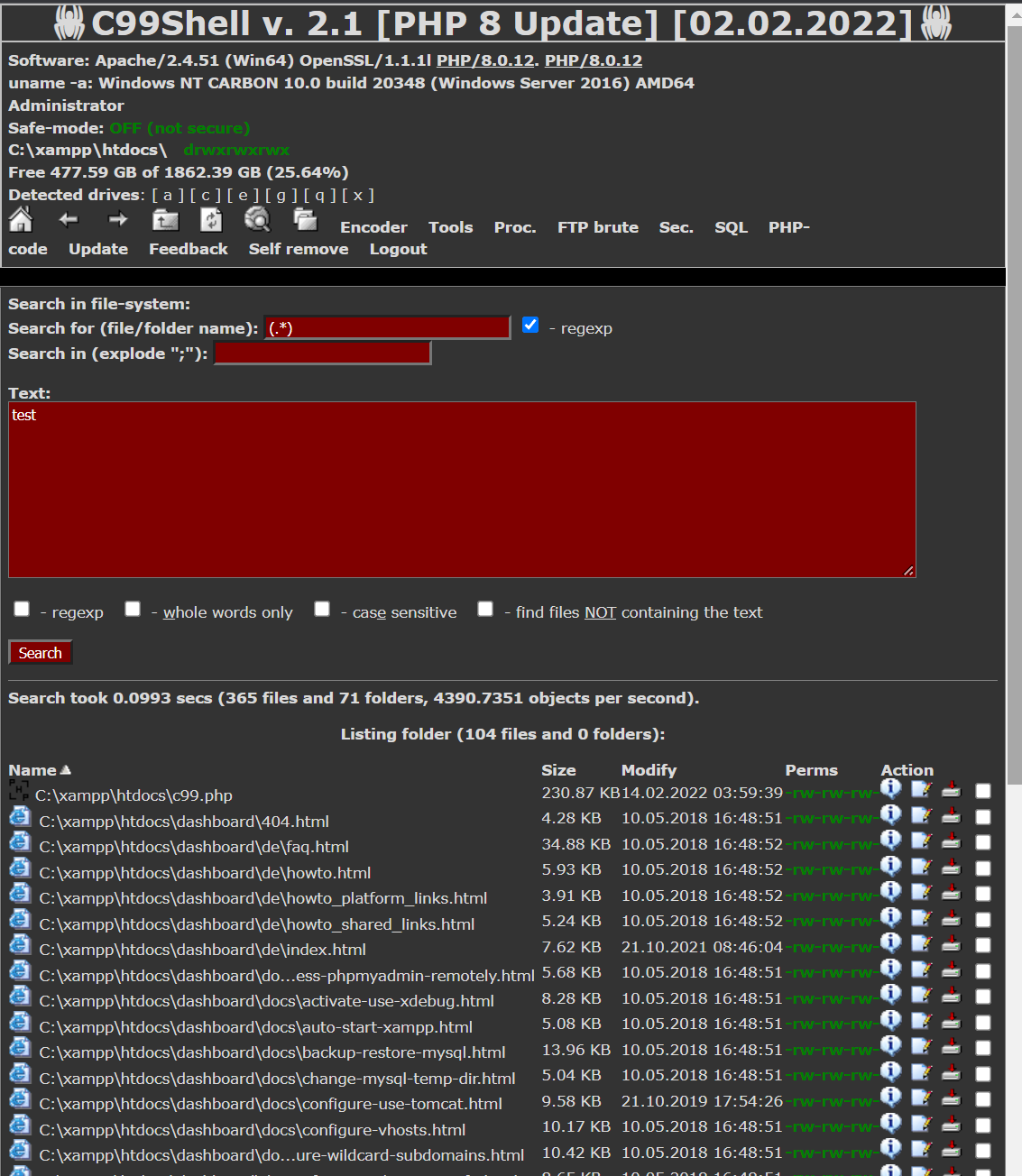
The c99 shell lets the attacker take control of the processes of the server, allowing him or her give commands on the server as the account under which the threat is operating. It lets the hacker upload, browse the file system, edit and view files, in addition, to deleting, moving them and changing permissions. Finding a c99 shell is an excellent way to identify a compromise on a system.
I've been testing php shells as part of my Ethical Hacking activities. This one is one of the oldest and best toys of my era which still has some use up to this day.
Sadly, the codes that I have is for PHP 5.3 and below. So I updated to the latest PHP8 version.
Here you go mates, a clean and safe-build version of the most stable c99shell.
This script is so old, It feels like I last used it ages ago. Even I started with a modern variant of this tool, I had to modify a lot of lines to make it work with php8.
I fixed the images, search feature, php code execution feature and many many other features
You can find my PHP8 version in my github repo
https://github.com/HolyOne/C99Shell-PHP8
Admin CyberSecurity